Not as it seems: Online Impostors
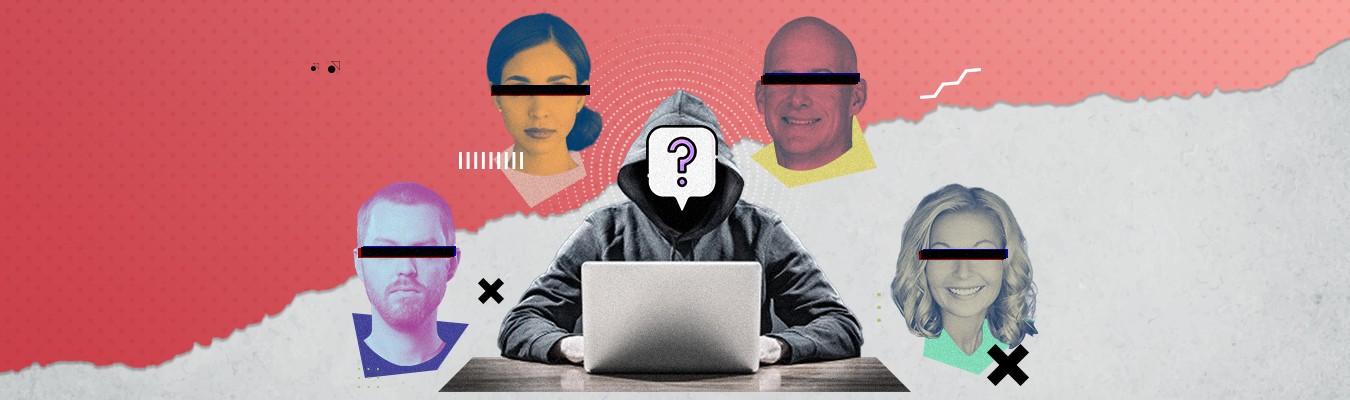
Not as it seems: Online Impostors
Date: 29 July 2020
With the COVID-19 pandemic still ravaging the world, people have been mostly relegated in their homes. Working from home has become increasingly the norm for workers who can do so. Even schools are mostly doing classes online with the Philippines exploring the idea of “blended learning” with the objective of keeping the students in their respective houses. With many aspects of our daily lives able to be done, and in fact, being done, at home, a number of businesses/professionals have capitalized on this and started to offer their services remotely. Nowadays consultations with lawyers, doctors, and a whole host of other professionals can be done online whether over the phone, messaging services, communications apps, or a dedicated app.

A problem now comes to mind, how sure are you that the person you are consulting or talking to is really licensed to practice the said profession, or worse is that person really the person he is claiming to be? The identity can easily be ascertained if consultations are made through video conferencing but is extremely hard for other forms of communication. In fact, there has been a proliferation of fake accounts using photos or names of real professionals and their details with the intention to defraud and deceive unsuspecting individuals over the net. How do you ensure that you are talking to a real professional? Here are some tips:
- ONLY DEAL WITH PROFESSIONALS THROUGH THEIR OFFICIAL PAGES OR PROFILES. YOU CAN ALSO CHECK THE HISTORY AND POSTS ON SAID PAGE TO ENSURE THAT THEY ARE LEGITIMATE.
- DON’T BE ASHAMED TO ASK FOR THE CREDENTIALS OF THE PROFESSIONAL YOU ARE CONSULTING. IF THEY ARE REAL PROFESSIONALS, THEY WON’T MIND SHOWING YOU THEIR CREDENTIALS.
- CHECK THE NAME AND THE VALIDITY OF THE PROFESSIONAL LICENSE WITH THE WEBSITE OF THE PROFESSIONAL REGULATION COMMISSION IN THE CASE OF PROFESSIONALS EXCEPT FOR LAWYERS WHICH YOU CAN CHECK WITH THE SUPREME COURT WEBSITE.
Following these steps does not fully eliminate the risk of you dealing with a fraudster but it greatly lowers it.
For the professionals, if you find out that someone is using your photo or name to offer professional services to the public, here’s what you can do:
- INFORM THE PUBLIC THROUGH POSTS IN YOUR OFFICIAL PAGES OR PROFILES THAT YOU ONLY OFFER SERVICES THROUGH SAID OFFICIAL PAGES OR PROFILES. INCLUDE A STATEMENT THAT ANY PAGE OR PROFILE USING YOUR PHOTO OR NAME OUTSIDE YOUR OFFICIAL ONES ARE LIKELY FAKE AND IF A PERSON DEALS WITH THEM, YOU ARE NOT LIABLE FOR IT.
- IF SOMEONE IS USING YOUR NAME OR PHOTO AND OFFERING PROFESSIONAL SERVICES TO THE PUBLIC, INFORM YOUR PROFESSIONAL ORGANIZATION AND THE PRC IMMEDIATELY.
- ASK THE SITE TO TAKE DOWN THE FAKE PAGE OR PROFILE. YOU CAN EXERCISE YOUR RIGHT TO ERASURE OR BLOCKING UNDER SEC. 16 (E) OF THE DATA PRIVACY ACT CONSIDERING THAT THE USE OF YOUR PHOTO AND NAME ARE UNAUTHORIZED AND THAT IT IS USED FOR UNAUTHORIZED PURPOSES.
- FILE A CASE FOR VIOLATION OF THE CYBERCRIME PREVENTION ACT, SPECIFICALLY SEC. 4 (B) (3) WHICH PUNISHED COMPUTER RELATED IDENTITY THEFT.
Note however, that when we post something and make it available to the public, there is no reasonable expectation of privacy for said posts. In the case of Vivares vs. St. Theresa’s College (G.R. No. 202666, 29 September 2014.) the Supreme Court, quoting with approval the case of United States vs. Maxwell (45 M.J. 406 [C.A.A.F. 199]) which states that "[t]he more open the method of transmission is, the less privacy one can reasonably expect. Messages sent to the public at large in the chat room or e-mail that is forwarded from correspondent to correspondent loses any semblance of privacy." In the same case, the Supreme Court also quoted the case of United States vs. Gines-Perez (214 F. Supp. 2d at 225) where the U.S. Supreme Court held, “[A] person who places a photograph on the Internet precisely intends to forsake and renounce all privacy rights to such imagery, particularly under circumstances such as here, where the Defendant did not employ protective measures or devices that would have controlled access to the Web page or the photograph itself. xxx [a] person who places information on the information superhighway clearly subjects said information to being accessed by every conceivable interested party. Simply expressed, if privacy is sought, then public communication mediums such as the Internet are not adequate forums without protective measures.” Simply put, absent any measures to limit access to an online post like when a post is made public, then it can be said that one should not expect a level of privacy over said posts. This is not to say that there is no other protections against unlawful or unauthorized use. As listed above, recourse can be made through the invocation of the Data Privacy Law and the Cybercrime Prevention Act.
In the end, we all need to be vigilant in our dealings over the internet especially given the fact that more often than not we do not see who we’re talking to. After all, nothing beats vigilance and, well, common sense.
Disclaimer: The information presented in this article is for informational purposes only. It should not be taken as legal advice or be used as a basis for legal action or defense.
